More than 100 companies are using insecure collaborative robots putting at risk tenths of thousands of workers and infrastructures around the world. These insecurities stem from the use of technology from Universal Robots (a company owned by Teradyne). Universal Robots technology is reportedly vulnerable and the manufacturer is proactively ignoring security after repeated security reports.
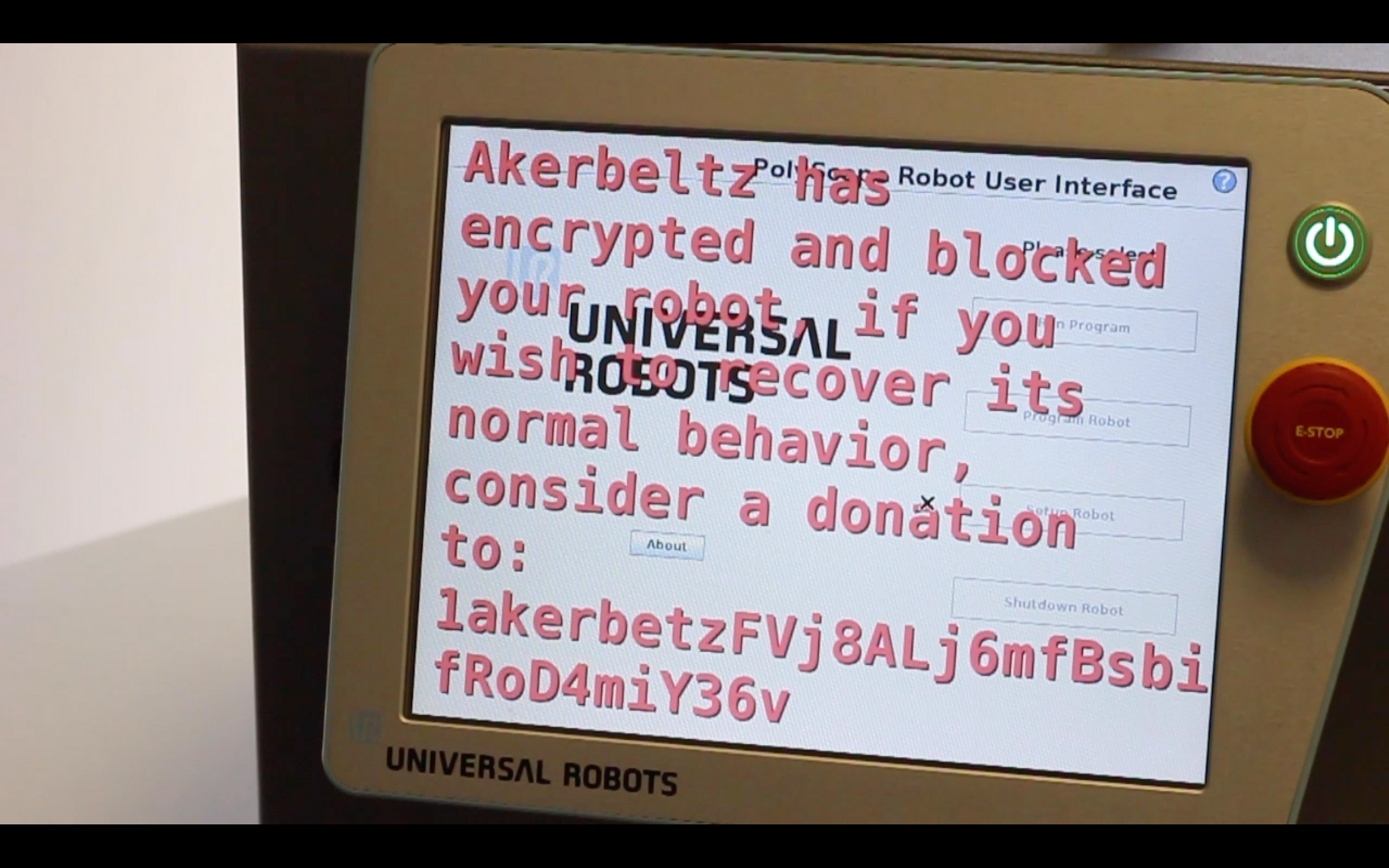
The culprits behind this insecure industrial robotics landscape are collaborative robots UR3, UR5, UR10, eUR3, eUR5, eUR10 and eUR16 (all manufactured by Universal Robots) which present dozens of unpatched security flaws over an insecure file system that's not updated nor maintained according to common security practices. The current security flaws can be exploited by physical and remote attack vectors and can enable cyber-criminals to interrupt the automation processes, encrypt or steal intellectual property in the robot (and/or connected vulnerable machines) or even incur in collisions after the attackers disable their safety mechanisms, which can be done remotely.
The current security flaws can be exploited by physical and remote attack vectors and can enable cyber-criminals to interrupt the automation processes, encrypt or steal intellectual property in the robot (and/or connected vulnerable machines) or even incur in collisions after the attackers disable their safety mechanisms, which can be done remotely.
Among the companies affected, it's easy to identify international automotive companies and suppliers including Ford (Romania), Nissan (Japan), Opel (Germany) , Bajaj (India), Alpha Corporation (Japan) or Continental (Spain). From farmaceutial companies to food an agriculture processing and production, these robots are used insecurely across domains including universities (e.g. PSG College of Technology) and hospitals (e.g. Copenhagen University Hospital, Gentofte Hospital).
According to the sources used, including the official case studies [1] information from the very own Universal Robots, more than 90.000 workers involved in these organizations might be subject to suffer from these security flaws and the lack of security awareness of this company from the Teradyne group. The more than 100 organizations spread around the world present an average employee count of more than 650, which significantly elevates the risks given the importance of insider threats, as reported by several articles and standards including NIST SP 800-82 Guide to Industrial Control Systems (ICS) Security [2].
Geographical situation
From the data availble, these insecure collaborative robots are operating in 31 countries with special representation in Denmark, Czech Republic, India and the USA.
| Country | # Companies affected |
|---|---|
| Australia | 1 |
| Austria | 2 |
| Canada | 2 |
| China | 2 |
| Czech Republic | 10 |
| Denmark | 12 |
| Finland | 2 |
| France | 6 |
| Germany | 13 |
| Iceland | 1 |
| India | 10 |
| Indonesia | 1 |
| Italy | 4 |
| Japan | 7 |
| Korea | 1 |
| Netherlands | 2 |
| New Zealand | 4 |
| Norway | 1 |
| Poland | 4 |
| Romania | 2 |
| Singapore | 3 |
| Slovakia | 1 |
| Slovenia | 1 |
| Spain | 5 |
| Sweden | 5 |
| Switzerland | 3 |
| Taiwan | 3 |
| Thailand | 1 |
| USA | 26 |
| United Kingdom | 2 |
| Vietnam | 1 |
Sectors affected
More than 16 sectors and areas of application are affected. The following table summarizes the data collected:
| Sector | # |
|---|---|
| Audiovisual media | 1 |
| Automotive | 9 |
| Automotive and Subcontractors | 15 |
| Automotive, Metal and Machining | 1 |
| Education | 2 |
| Electronics and Technology | 18 |
| Home care, personal care, oils | 1 |
| FMCG, Pharma and Chemistry | 1 |
| Food, Beverage and Agriculture | 11 |
| Furniture and Equipment | 9 |
| Healthcare | 1 |
| Metal and Machining | 38 |
| Pharma and Chemistry | 7 |
| Plastic and Polymers | 15 |
| Scientific and Research | 6 |
| Textile industry | 1 |
Conclusions
It must be noted that the data available represents only a subset of the actual insecurity landscape. According to latest reports, Universal Robots has sold more than 42,000 robots that present critical vulnerabilities [3] [4] [5] [6] as of latest firmware. A complete list of the companies affected is available below:
Complete list of companies affected according to data available (produced automatically)
2K Trend, a.s.
AGH University of Science and Technology, Poland
Aircraft Tooling Inc.
Albrecht Jung GmbH und Co. KG
All Axis Machining
ALPHA Corporation
AQUAEL
AR+
ASSA ABLOY NZ
ASSA ABLOY RO
Atria
Attl a spol. s.r.o. Továrna na stroje
Aurolab
Autodesk
-
Babo Arms
Bajaj Auto
BAUMRUK & BAUMRUK
Beijing BAI Lear Automotive System Co., Ltd.
Benchmark Electronics Thailand
Betacom
beyerdynamic GmbH & Co. KG
-
Blue Star Limited
Böco Böddecker
BOOG
BTC Mold CO., LTD
BWIndustrie
Carl Zeiss
Cascina Italia
Clamcleats Ltd
Clearpack Group
CNC Trčka
Comprehensive Logistics
Continental Automotive Spain
Coty Cosmetics
COVAP
Craft and Technik Industries (CATI)
Creating Revolutions
Darex
DCL Logistics
Technical College of Jutland
Dynamic Group
EMTEK
Endutec GmbH
Etalex
EVCO Plastics
Ferdinand Wagner Profile
Fluidics Instruments B.V.
FME Feinmechanik AG
Ford Motor Company
Franke Küchentechnik AG
Fries Maschinenbau
FT produktion
Fusion OEM
Copenhagen University Hospital, Gentofte
Gern Glas
GKN Driveline
Glidewell Laboratories
Group PSA
Gustav Hensel GmbH und Co. KG
-
Heemskerk Fijnmechanica B.V.
Hofmann Glastechnik GmbH
Huis Ten Bosch Co.,Ltd.
Hyundae Induction Hardening Heat Treatment (HIHHT)
InPrint A/S
iQLANDIA Science Center
Izoelektro d.o.o.
Jenny | Waltle GmbH
-
Konetehdas K&K
Koyo Electronics Industries
Lear Corporation
LEAX Group
Life Elettronica Srl
Linaset
Linatex
L'Oréal India Private Limited
Magneti Marelli Slovakia
MANN+HUMMEL Ibérica
Marka S.r.l.
Melecs EWS GmbH
Minitüb
Mjolkursamsalan Akureyri
-
New Engineering Works
Nichrominox
Nippon Zettoc
Nissan Motor Company
Nordic Sugar
Nortura
Nymann Teknik
Opel
Orkla Foods Sverige
Oticon
OTV Plast
Paradigm Electronics.
PLC Industries
PMI
Profatec AG
Prysm Industries
PSG College of Technology
PT JVC Electronics Indonesia
RAMTEC (Robotics & Advanced Manufacturing Technology Education Collaborative).
RCM Industries
-
RNB Cosméticos
Ronet
RSS Manufacturing and Phylrich
Xiamen Runner Industrial Corporation
RUPES
SANOFI
Scandinavian Tobacco Company
Scott Fetzer Electrical Group.
SHAD
Shruti Engineers
Sky Engineering
SMEW Textile Machinery Pvt. Ltd.
STAMIT s.r.o.
Stantræk
Talbot Technologies
Task Force Tips
TCI New Zealand
Thiele
thyssenkrupp Bilstein
Tool Gauge
Toolcraft Inc
Trelleborg Sealing Solutions
T&W Stamping
Unilever
Vinacomin Motor Industry Joint Stock Company
-
Voodoo Manufacturing
Whippany Actuation Systems
Yokota Corporation
YUEYIN Technology
Zippertubing Company
As indicated by Kirschgens et al. [5:1] in 2018, robots are increasingly intertwined with other facets of IT and envisioned to get much more autonomy, interacting physically with humans yet, robot security is being ignored by manufacturers. The present article illustrates this claim with evidence collected over the last two years of research in the area.
Acording to many, cobots are at the rising point of are the robotics technological revolution and hand in hand with Industry 4.0, called to change many industrial operations while influencing greatly the professional and consumer sectors. From the words of [5:2]:
we find extremely relevant to promptly alert about the imperative of ensuring a security first approach now, before new devices continue being irresponsibly rushed to the market by a number of companies. Likewise, we encourage all sides involved to develop both internal and external policies aimed at the adequate management of some of the safety and security issues
My past 10 years building robots and my daily work at Alias Robotics provides an interesting angle. From preliminar data and customer responses, it seems most of these groups are not aware of the insecurities that these robots present to them. This short essay puts this matter into perspective, and hopes to generate additional awareness across users of the robots.
To conclude, I'd once again cite Kirschgens et al. [5:3] and repeat the main question that the authors asked themselves back in 2018:
How long will it take until manufacturers notice the damages that the insecurity of these devices may cause and act? ... it seems decisive to remind that, in a world where IT and robotics are increasingly intertwined, safety and security are necessarily tightly coupled. A security-first approach is ”sine qua non” requisite for ensuring safe operations with robots.
References
Universal Robots. Automate virtually anything. Universal Robots case studies https://www.universal-robots.com/case-stories/ ↩︎
Stouffer, K., Lightman, S., Pillitteri, V., Abrams, M., & Hahn, A. (2014). NIST special publication 800-82, revision 2: Guide to industrial control systems (ICS) security. National Institute of Standards and Technology. ↩︎
Cerrudo, C., & Apa, L. (2017). Hacking robots before skynet. IOActive Website, 1-17. ↩︎
Mayoral-Vilches, V., Juan, L. U. S., Carbajo, U. A., Campo, R., de Cámara, X. S., Urzelai, O., ... & Gil-Uriarte, E. (2019). Industrial robot ransomware: Akerbeltz. arXiv preprint arXiv:1912.07714 https://arxiv.org/pdf/1912.07714.pdf ↩︎
Kirschgens, L. A., Ugarte, I. Z., Uriarte, E. G., Rosas, A. M., & Vilches, V. M. (2018). Robot hazards: from safety to security. arXiv preprint arXiv:1806.06681 https://arxiv.org/pdf/1806.06681.pdf ↩︎ ↩︎ ↩︎ ↩︎
Alias Robotics. Week of Universal Robots' bugs. https://news.aliasrobotics.com/week-of-universal-robots-bugs-exposing-insecurity/ ↩︎


